What is OPSEC?

OPSEC (Operational Security) is the structured method for denying adversaries the information necessary to identify, locate, or harm you. Encryption protects message content; OPSEC protects context. While Tor masks your network identity, OPSEC ensures that your behavioral patterns, language, timing, metadata, and digital habits don't create a composite fingerprint that can be traced back to your real identity.
The distinction is critical: you can use Tor Browser perfectly, encrypt every message with PGP, pay exclusively in Monero, and still be identified if your OPSEC is weak. Ross Ulbricht (Silk Road) used state-of-the-art encryption but was caught through a single reused username. Alexandre Cazes (AlphaBay) ran the largest darknet market in history but was identified through a personal email address in server error messages. Technology protects data. OPSEC protects humans.

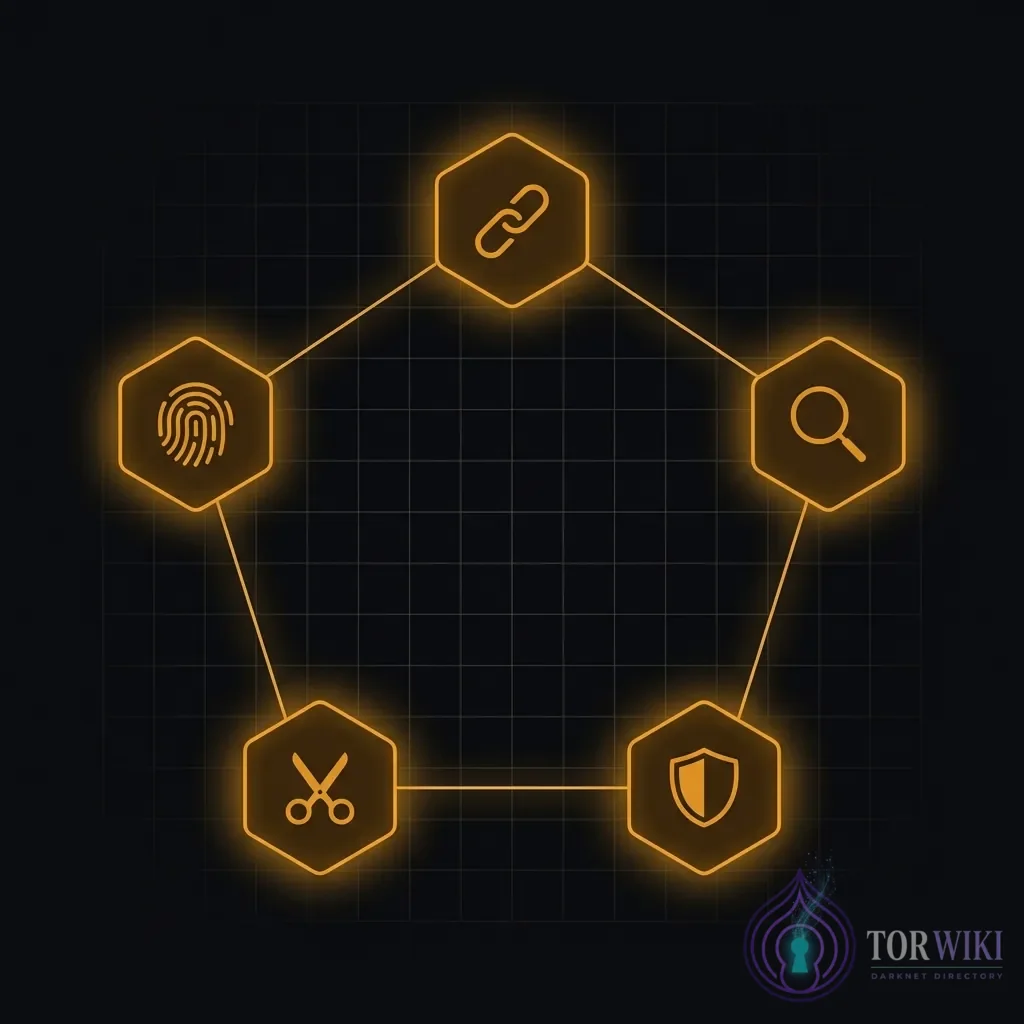
The Five Pillars of OPSEC
1. Separation
Maintain complete, absolute separation between your clearnet identity and dark web persona. This means separate hardware, separate accounts, separate communication channels, and — critically — separate mentality. Never log into a personal account (Gmail, social media, banking) from the same machine, network, or session used for anonymous activity. A single cross-contamination event can permanently link your identities.
- Hardware: Use a dedicated device — ideally a secondhand laptop purchased with cash. Never use your primary computer.
- Network: Use public Wi-Fi, a separate mobile hotspot, or a VPN. Never your home network directly.
- Accounts: Generate unique email addresses, usernames, and passwords for every anonymous platform.
- Payments: Monero acquired through non-KYC channels. Never use cryptocurrency purchased from exchanges linked to your verified identity.
2. Consistency
The "Grey Man" principle: be so predictable and unremarkable within your assumed persona that you become invisible in the noise. If your persona is a developer from Berlin, you cannot suddenly use Texas slang, post during US business hours, or reference the NFL. Any inconsistency is a thread an adversary can pull to unravel the entire fabrication. Consistency means discipline — maintaining a persona through every interaction, every message, every forum post, even under pressure.
3. Compartmentalization
Treat all activities as isolated intelligence cells. Create unique usernames, PGP keys, Monero sub-addresses, and communication channels for every platform and activity. If one identity is compromised ("burned"), the others remain protected because there is no link between them. This is the operational model used by intelligence agencies worldwide — and it works because it limits the blast radius of any single failure.
4. Minimization
The less data you generate, the less can be weaponized against you. Never share age, hobbies, geographic location, profession, political opinions, or personal anecdotes. Under "Mosaic Theory", small, seemingly insignificant details — your timezone, a regional dialect word, a reference to local weather — can be pieced together by an analyst to construct a surprisingly accurate profile. Each detail individually reveals nothing; combined, they reveal everything.
5. Verification
The dark web operates on zero trust. Verify all .onion URLs from multiple independent trusted sources. Confirm PGP key fingerprints through out-of-band channels. Check market warrant canaries regularly. The evolution of phishing and impersonation attacks in 2025-2026 — including AI-generated clone sites and deepfake admin impersonation — makes verification more critical than ever. Trust nothing by default; verify everything through cryptographic means.
Common OPSEC Failures
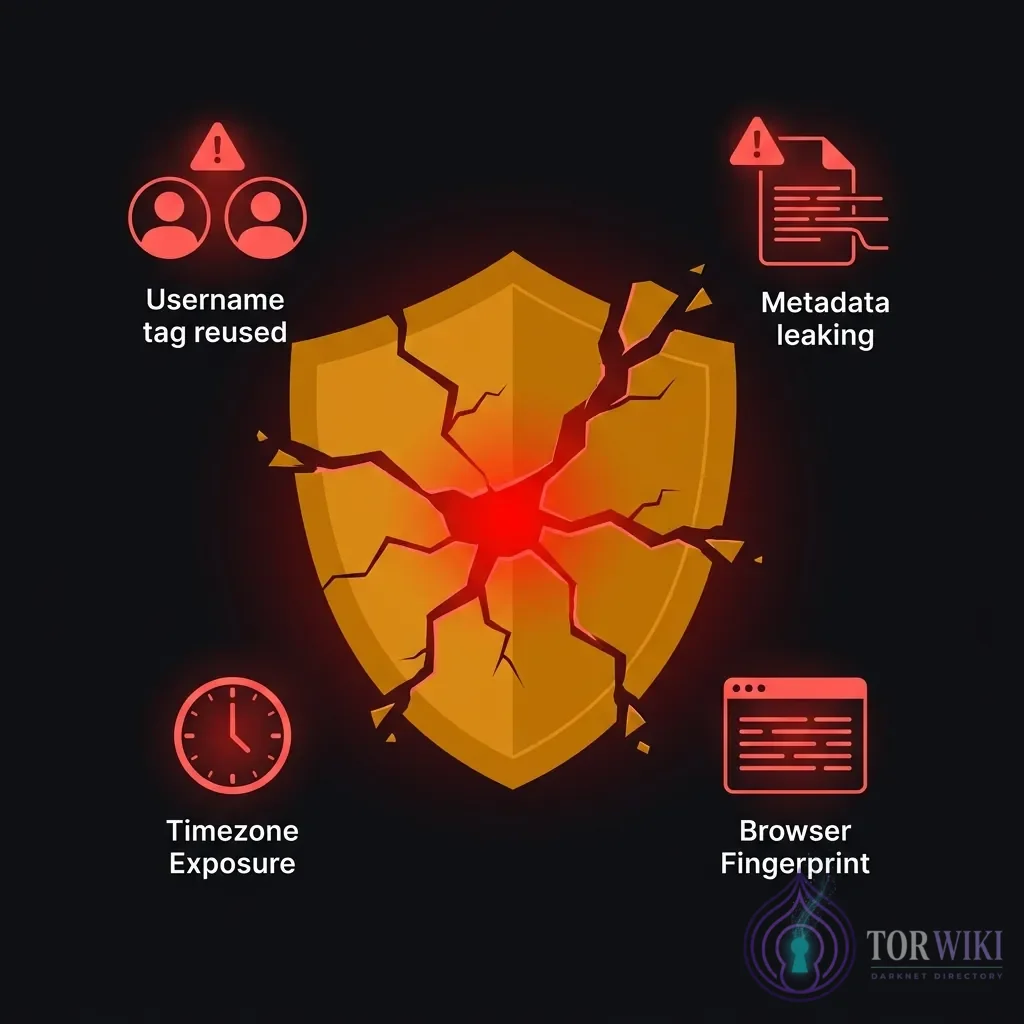
Reusing Usernames
OSINT tools like SpiderFoot, Maltego, Sherlock, and WhatsMyName can search years of archived web data to connect "anonymous" usernames back to real email addresses, social media accounts, or code repository profiles. One reused handle — even one used briefly years ago — can unravel an entire identity. The CIA's Marble Framework documents reveal that state-level actors maintain comprehensive username correlation databases.
Metadata in Files
Files carry invisible fingerprints. JPEGs contain EXIF data (GPS
coordinates, camera serial numbers, timestamps), Word documents embed author
names and revision history, PDFs can contain creation software
identifiers. Use mat2 on Tails OS or exiftool to
scrub every file before uploading or sharing. A single unstripped photo has led to
multiple darknet arrests — the metadata trail is often more damaging than the
content itself.
Time Zone Leaks
Posting patterns reveal your geographic location with surprising precision. Consistent online/offline cycles correlated with circadian rhythms and local time zones allow adversaries to narrow your physical location to a region. Mitigation: schedule posts at random times, use queuing tools, or deliberately offset your activity patterns.
Writing Style (Stylometry)
AI-augmented stylometric analysis can identify writing similarities across platforms with high confidence. Unique phraseology, punctuation habits (em-dashes vs hyphens), sentence length patterns, vocabulary frequency distributions, and topic-specific terminology create a linguistic fingerprint as unique as a physical one. Counter-measures include translation chaining (write in English — translate to Russian — translate back), using style-normalization tools like Anonymouth, and deliberately varying your writing patterns.
Browser Fingerprinting
Beyond IP addresses, browsers leak a constellation of identifying data: screen resolution, installed fonts, WebGL rendering, canvas fingerprint, audio context, and timezone settings. In combination, these create a device fingerprint that is unique across millions of users. Tor Browser mitigates this through standardized window sizes and disabled APIs — but only if you don't maximize the window or alter default settings.
Real-World Case Studies

1. Silk Road - Username Reuse (2013)
Ross Ulbricht used the alias "altoid" on both darknet forums and public
Bitcoin discussion boards. On one public board, he posted his real Gmail address
(rossulbricht@gmail.com) while promoting Silk Road under the altoid handle.
FBI investigators linked the anonymous founder "Dread Pirate Roberts" to Ulbricht
through this single username connection. One forum post destroyed a multimillion-dollar
empire. Lesson: Never use any handle, email address, or identifier
across both anonymous and real-world contexts.
2. AlphaBay - Personal Email in Server Config (2017)
Alexandre Cazes operated AlphaBay — the largest darknet market at the time, with
400,000 users. His fatal OPSEC failure: the platform's welcome email was sent from
pimp_alex_91@hotmail.com, a personal Hotmail address that appeared in the
server's error messages. Investigators traced the email to Cazes's real identity,
linking him to server hosting payments, cryptocurrency holdings, and luxury real estate
in Thailand. Lesson: Never use personal accounts, email addresses, or
identifiers in any server configuration, error handling, or automated communication.
3. Hansa Market - Law Enforcement Honeypot (2017)
Following AlphaBay's seizure (Operation Bayonet), Dutch National Police had already covertly seized control of Hansa Market and operated it for 27 days. During this period, they planted tracking technologies in file downloads, harvested user credentials, modified the site to capture additional metadata, and recorded all transactions and communications. Thousands of users who migrated from AlphaBay to Hansa unknowingly walked into a government-operated honeypot. Lesson: After any major market shutdown, assume all surviving markets are potentially compromised. Wait, verify, and proceed with extreme caution.
4. Kingdom Market - Server Misconfiguration (2023)
Kingdom Market was seized after investigators discovered that misconfigured server headers leaked the real IP address of the backend infrastructure. This single technical error bypassed all other security measures, providing law enforcement with the physical location of the servers and ultimately the administrators. Lesson: Server-level OPSEC is as critical as personal OPSEC. A single misconfigured HTTP header, logging setting, or error page can expose an entire operation.
5. The "Sabu" Case - Time Zone Leak (2012)
LulzSec hacker Hector Monsegur ("Sabu") maintained operational activity that consistently dropped during East Coast US sleeping hours. The FBI correlated his online/offline patterns with New York timezone, narrowing the search area and contributing to his identification and arrest. Lesson: Your activity patterns are metadata that reveals location. Randomize activity timing or use scheduling tools.
6. The Ochoa Case - Photo Metadata (2012)
A hacker posted a provocative photo online without stripping GPS metadata from the EXIF
data. The embedded coordinates led police directly to the photographer's home
address. The arrest took less than 24 hours from the photo's publication.
Lesson: Always strip metadata from files using mat2,
exiftool, or Tails OS's built-in metadata scrubbing before sharing
anything.
7. The Unabomber - Stylometry (1996)
Ted Kaczynski was identified because his brother recognized specific phrases and linguistic quirks in the published "Manifesto" that matched personal letters and family correspondence. The phrase "you can't eat your cake and have it too" — an unusual inversion of the common idiom — was a key identifier. Modern AI can perform this analysis across millions of text samples in seconds. Lesson: Your writing style is a biometric identifier. Use active counter-measures for any sustained anonymous writing.
Digital Forensics: What Law Enforcement Can Extract
Understanding adversary capabilities is essential for calibrating your OPSEC. When law enforcement seizes a device or gains access to network traffic, they can extract:
| Source | What's Extracted | Defense |
|---|---|---|
| Seized Devices | Full disk contents, browser history (even "deleted"), RAM contents (cold boot attacks), SSD wear-leveling artifacts that preserve "deleted" data | Full-disk encryption (LUKS/VeraCrypt), Tails OS (RAM wipe on shutdown), hardware destruction if seizure is imminent |
| Network Traffic | Timing correlation attacks (matching Tor entry/exit timestamps), traffic volume analysis, DNS leak capture | VPN before Tor, bridges for entry, avoid sustained high-bandwidth activity that creates timing patterns |
| Cryptocurrency | Chainalysis/CipherTrace can trace BTC transactions across mixers. Monero is significantly harder but not guaranteed immune — heuristic analysis improves annually | Use Monero (XMR) exclusively. Acquire through non-KYC channels. Use unique sub-addresses for every transaction. |
| Social Engineering | Compromised associates, informants, undercover agents operating in forums and markets | Zero-trust policy. Verify PGP-signed canaries. Never share personal information regardless of perceived trustworthiness. |
| OSINT (Open Source) | Username correlation, writing style matching, social media cross-referencing, public records | Unique identities per platform, style variation, strict information minimization |
Communication OPSEC
PGP Key Management
- Generate keys on an air-gapped device — never create PGP keys on a network-connected machine
- Use subkeys for daily operations — keep the master key offline. If a subkey is compromised, the master key and other subkeys remain safe.
- Set key expiration — 1-year expiry forces regular rotation and limits the window of compromise
- Publish keys through multiple channels — key servers, Dread profile, market profile. Cross-referencing prevents impersonation.
Secure Messaging Comparison
| Platform | Protocol | Metadata Protection | Best For |
|---|---|---|---|
| Session | Signal Protocol (modified), decentralized | No phone number required. Onion-routed. Minimal metadata. | General anonymous communication |
| SimpleX | Double-ratchet, no user identifiers | No user IDs at all — connection-based. Strongest metadata protection. | Maximum privacy requirements |
| XMPP + OMEMO | OMEMO (multi-device Signal protocol) | Depends on server. Self-hosted XMPP with Tor provides strong protection. | Technical users willing to self-host |
| Briar | Custom P2P protocol | Direct peer-to-peer over Tor. No servers involved. Works offline via Bluetooth/Wi-Fi. | Protest environments, high-surveillance contexts |
Warrant Canary Verification
A warrant canary is a PGP-signed statement published periodically by a market or service, declaring that they have not received a government subpoena or gag order. If the canary stops being updated or the PGP signature is invalid, assume the platform is compromised. Always verify canary signatures independently — don't trust the platform's own verification tool, as it could be modified during a covert takeover.
Physical OPSEC
- Delivery address strategy: Never use your home address. Consider PO boxes, alternative addresses, or locations where you can plausibly deny ordering the package.
- Faraday pouches: Store devices in Faraday bags when not in use to prevent remote access, location tracking, and microphone activation.
- Clean room principles: Handle packages with gloves. Dispose of packaging in public bins away from your location. Never leave packaging in your home trash.
- USB security: Never plug unknown USB devices into any machine — BadUSB attacks can compromise a computer in seconds through a device that appears to be a standard flash drive.
- Device disposal: When disposing of a device used for anonymous activity, destroy the storage media physically. Overwriting is insufficient for SSDs due to wear-leveling. A hammer or drill through the NAND chips provides the strongest guarantee.
Your OPSEC Checklist
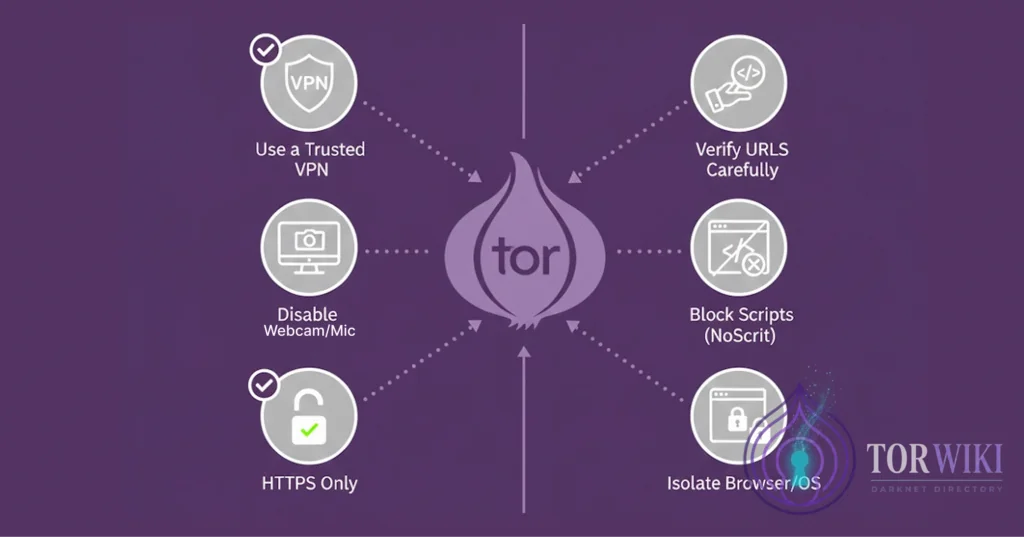

Before Going Anonymous
- Hardware isolation — dedicated device purchased with cash, never used for personal accounts
- Network hygiene — public Wi-Fi, mobile hotspot, or VPN. Never home IP directly.
- Clean OS — Tails (USB boot) or Whonix (VM). No consumer telemetry.
- Close all other applications — reduce attack surface, prevent clipboard leaks
- Verify VPN connection and check for IP/DNS leaks at
ipleak.net - Disable smartphone in the room — phones are tracking vectors (cell tower triangulation, ultrasonic beacons)
During Anonymous Sessions
- Tor Browser security level set to "Safest" (JavaScript disabled)
- Only use trusted directories and PGP-verified links
- Maintain persona consistency — no real-world references, no personal anecdotes
- Strip metadata from all files before uploading (
mat2orexiftool) - Use PGP encryption for all sensitive communications
- Never copy-paste between anonymous and personal contexts
- Monitor for abnormal behavior — unexpected CAPTCHAs, new login prompts, or interface changes may indicate platform compromise
After Anonymous Sessions
- Full shutdown of Tails OS — triggers automatic RAM wipe, erasing all session data
- Store USB drive in encrypted storage or Faraday pouch
- Never leave devices in sleep mode — Cold Boot Attacks can extract encryption keys from RAM that hasn't been properly cleared
- Clear any clipboard contents on your host machine
- Disconnect VPN after Tor is fully closed
Advanced Techniques
Cryptocurrency Privacy
Bitcoin is pseudonymous, not anonymous. Every BTC transaction is permanently recorded on a public blockchain. Chain analysis firms like Chainalysis and CipherTrace can trace funds across mixers, tumblers, and exchanges with increasing accuracy. Monero (XMR) uses ring signatures, stealth addresses, and confidential transactions to make sender, receiver, and amount opaque by default. Regardless of cryptocurrency choice, your transaction privacy ultimately depends on endpoint behavior — how you acquire, store, transfer, and spend coins.
Social Engineering Defense
Implement a zero-trust policy: never share personal information regardless of perceived trustworthiness, rapport, or authority claims. Verify administrator messages via PGP-signed canaries on official channels. Be aware that law enforcement uses social engineering as a primary investigative technique — undercover agents build relationships over weeks or months before attempting information extraction.
Threat Model Assessment
| Level | Threat | Protocol |
|---|---|---|
| Low | ISP monitoring, casual surveillance | VPN + Tor Browser + JavaScript disabled. Sufficient for research and browsing. |
| Medium | Corporate surveillance, journalist protection | Tails OS + PGP + Monero + no personal identifiers. No persistent storage. |
| High | State-level actors, intelligence agencies | Dedicated hardware (cash-purchased) + Qubes-Whonix + Monero via non-KYC + linguistic masking + public Wi-Fi + Faraday storage + physical OPSEC |
Most users overestimate their required threat level, leading to unnecessary complexity that creates its own risks (misconfigured tools, forgotten procedures). Honestly assess your actual threat model and implement the appropriate protocol consistently. A simple protocol followed rigorously is more secure than a complex protocol followed inconsistently.